By Lieutenant Colonel Jose M Rufas, Chief of Attack the Networks Branch, C-IED Centre of Excellence
“Analysis is the art of creation through destruction.”
(P.S. Baber, in his book “Cassie Draws the Universe” first published in 2010)
Unfortunately, most of the would-be subject matter experts in countering improvised explosive devices (C-IED) are ingenuously content with the reactive and obsolete approach to the matter under the direct responsibility of military engineers and explosive ordnance disposal (EOD) units, headquarters and organizations. The author is also a widely experienced Military Engineer and EOD Operator, but please accept his sincere apologies for the following statement: that described approach is much closer to some sort of “explosive hazard reduction” or even “extended explosive ordnance search and clearance” than to the real (and potentially effective) “C-IED”1 one.
If you would initially not believe it, just take an overall look at those military collective exercises which are currently categorized as “C-IED exercises”: e.g. “Northern Challenge”, “Ardent Defender”, “Ravens Challenge”, “Bison Counter” … they are merely EOD exercises with a limited Technical Exploitation flavor!
The typical understanding of C-IED is mostly based on analysis of databases of past IED events, defensive posture against generic enemy tactics-techniques-procedures, search and clearance tasks, and force protection measures at a low-tactical level.
All of that is maybe forgetting that the main pillar of an effective C-IED approach should be the Attack the Networks one 2 .
It is not only the Allied doctrine which is reflecting that C-IED is much more than something only based on Defeat the Device and Prepare the Force pillars. The United Nations Institute for Disarmament Research (UNIDIR) states that for them the term C-IED or Counter-IED “… is used in its broadest possible context and includes all activities a State may undertake to prevent and mitigate the use of IEDs. Components of Counter-IED capability are divided into two broad categories: upstream components, which are focused on those activities aimed at deterring or preventing IED events from taking place, and downstream components, which are associated with responding to a particular IED event or mitigating an IED event should it occur. 3 ”
Even the European Union is also adopting the NATO concept for C-IED, as the European Defence Agency (EDA) has no specific doctrine but takes the Allied one as a reference.
Rien n’est plus dangereux qu’une idée quand on a qu’une idée 4
At a first sight, and from a relative ignorance of the reality, it could seem that the threat derived from IEDs or terrorism is not a big problem to face anymore… that opinion could may be somewhat acceptable when coming from politicians (highly interested in publicizing their successful management of security) or from the public society (only receiving the information that public media are willing to show to them).
What is really worrying is the perspective on the current and future threat from violent extremist organizations (VEO) that military and law enforcement authorities are evidencing through several thoughts and statements as follows:
- As the West is not suffering attacks with weapons and explosives in the homeland, there is almost no threat.
(Answer? There are no attacks due to the fact that numerous plots in Europe are dismantled by now, although not publicized due to political reasons). - As the military forces are not suffering casualties in areas of operations, there is almost no IED, terrorist or insurgent threat to analyze, to fight or to train against.
(Answer? If we are not deploying combat forces or are only training host nations, it would be hard to have casualties due to IED or terrorist attacks…). - The current or future areas of operations for NATO are not going to include IED, terrorist or insurgent threats, so C-IED would not be necessary anymore.
(Answer? NATO Strategic Concept 2023 includes terrorism and non-state actors as main threats, and current scenarios such as Ukraine or Sahel/West Africa are having a huge use of IEDs and improvised weapon systems). - The global Jihad is not existing anymore, so Al Qaeda and DAESH are almost not a threat anymore.
(Answer? This is not what their propaganda and forums are currently saying, and several groups connected with Daesh in Khurasan and Caucasus Provinces have been discovered inside Europe during last months).
Obviously, the extended ignorance among security and defense professionals about how the attacks with explosives or firearms are avoided (so through a proactive C-IED Attack the Networks approach) is logically making them only to consider the reactive approach (C-IED Defeat the Device and Prepare the Force).
We are sometimes even witnessing how the EOD teams are being reduced in numbers and manning, and how the authorities ́ support to equipment, updates, education, and training is also suffering…
Countering Threat Networks, Attack the Networks, and other… chimeras?
The successive Attack the Networks (AtN) functional processes5 are described as follows:
- Include the C-IED related problem in the mission.
- Understand the human terrain/environment in areaof operations.
- Understand the threat related to human networks.
- Identify/understand human networks.
- Analyze human networks ́ factors.
- Estimate the intended effects by the actions from human networks.
- Identification and analysis of own vulnerabilities.
- Analysis and organization of own means potentially supportive to AtN.
- Support to Targeting – preparation for network engagement.
- Targeting coordination/synchronization – effects integration.
- Conduct Targeting/network engagement.
- Evaluation of own effects – assessment.
- Analysis of counter effects from human networks.
- Evaluation of adversary effects – assessment.
- Analysis of the status of human networks ́capabilities.
- Refine intelligence needs.
- Refine effects requirements.
From the military perspective, one of the big problems of developing an effective Attack the Networks approach is mainly based on a set of intelligence education, processes and tools which have been designed for conventional threats and forces from state actors. A secondary relevant inconvenience is behind a Targeting process which has also been designed against conventional forces from an air force centric perspective, along with being mostly applicable to physical targets from adversary actors, and excessively focused on achieving lethal effects and conducting kinetic actions…
But in fact, the main obstacle to effectively plan, apply, and evaluate Attack the Networks initiatives over all kinds of human networks (friendly, neutral and adversary ones) against non-state actors (although sometimes sponsored by state actors) is a relative6 lack of specific (and updated) specialists, education, training, tools, tactics, techniques and procedures in both the Intelligence and Operations/Plans environment.
Don’t let your tools become your process…
If we must select the essential (so not all of them) activities for an effective and modern Attack the Networks strategy, they could be listed as follows:
- Analysis of network dynamics connected with area of Intelligence Interest.
- Human network characterization.
- Estimation and analysis of own critical capabilities and vulnerabilities.
- Identification, analysis, and prioritization of essential capabilities of human networks.
- Identification, analysis, and prioritization of critical vulnerabilities of human networks.
- Confrontation of own critical capabilities and vulnerabilities with adversary critical capabilities and vulnerabilities.
- Target System Analysis fully adapted to non-state actors.
- Scientific approach to target validation and prioritization from effects perspective.
- Integration of effects.
- Assessment of own effects and adversary effects.
For many years, we have counted on the “Counter Terrorism Analytical Framework” (CTAF) as the unique reference to identify the capabilities of a threat network. It was a quite useful reference tool, but it is only based on a single adversary human network, as some brands of Al Qaeda in late 20th Century (see Figure 1).The main problems when taking CTAF as the tool for defining critical capabilities of a human network are its basing on a very specific threat network, and maybe a strong bias from the authors…

Figure 1: Counter Terrorism Analytical Framework CTAF. (Source – US DoD Joint Publication JP-3.26 Counterterrorism)
…don’t let your process becomes your only tool.
As said before, the Target System Analysis (TSA) poses an essential process: its aim is to determine enemy vulnerabilities and exploitable weaknesses, along with what effects will likely be achieved against target systems and their associated activities. But TSA is simultaneously a systematic approach, a product, and a process. As a process, TSA entails identifying, describing, and evaluating the composition of an adversary target system to determine its capabilities, requirements, and vulnerabilities.
But again, there is a problem: current TSA was air force-centric designed for targeting conventional forces, so it is not that applicable to adversary non- state actors, while not useful for neutral or friendly human networks at all…
Additionally, there are no developed procedures for TSA on human networks or any effectively scientific approach to it at all… so all the effort and responsibility must lay on the analyst him(her)self, just based on individual intellect, experience, imagination… and for sure personal or collective bias!
As an example, we could analyze the most typical methodologies for analysis and prioritization of targets:
- CARVER (Criticality, Accessibility, Recuperability, Vulnerability, Effect and Recognizability)
- BARRIL (Benefit, Accessibility, Replaceable, Reconcilable, Influence, Leverage) (see Figure 2).
In fact, CARVER was developed during the Second World War as a quantifiable method for selection of targets in support to the agents working with the resistance inside territory occupied by Germany; it was refined during the Vietnam War, and it is still used as a methodology for target analysis and vulnerability assessment.
Both CARVER and BARRIL are considering too few criteria to absorb bias or mistakes, and the assignment of value is too subjective, confusing, and not quite clear, which could make the result vary widely from different analysts.
Nonetheless CARVER is much more useful for vulnerability assessment, and it was designed for conventional targets and lethal actions, which makes it inadequate for non-state actors.
Life is as full of problems as full of solutions as well.
From the perspective of Attack the Networks, the Counter Terrorism Analytical Framework (CTA) is too generic to identify and study the capabilities of a human network, so it would be better to:
- Create a more complete generic framework for human networks’ factors and capabilities, able to frame all kinds of potential adversary human networks to analyze.
- Create about twenty different categories of potential adversary human networks, selecting their characteristic factors and capabilities among the whole catalog of them as expressed in the generic framework.
- Pre-identify those factors (in black, figure 3) and capabilities (in maroon, figure 3) which could be initially more able to be subject to effects positive to us, along with those which could be less sensitive to the effects as derived from our actions (see Figure 3).
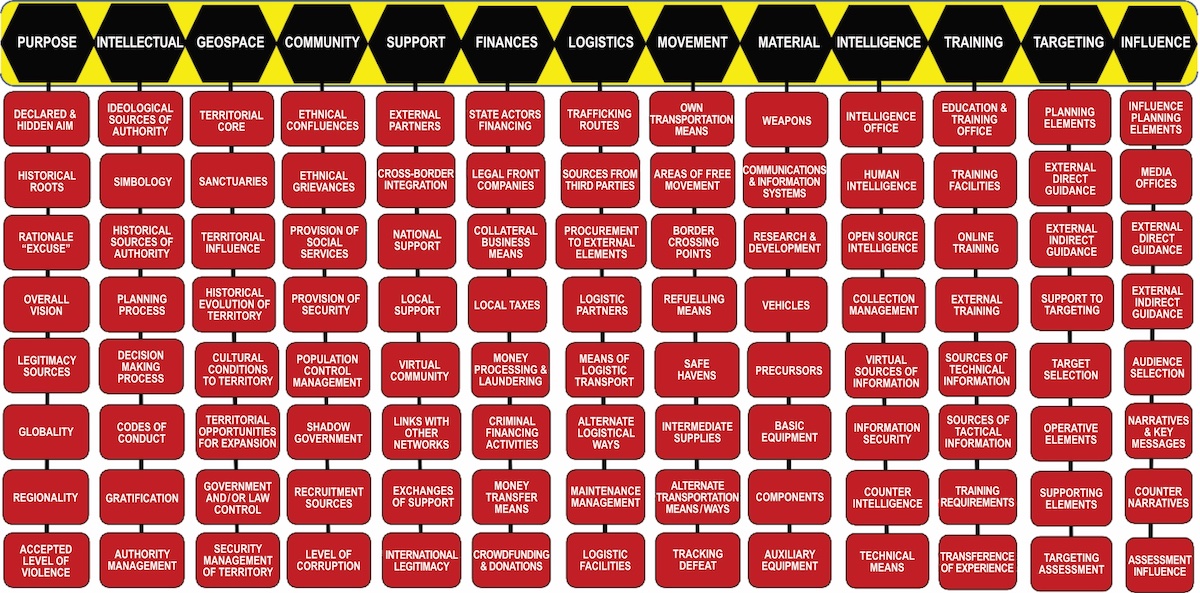
Figure 3: Generic framework for adversary human networks factors and capabilities. (Source – C-IED CoE)
In fact, and although some generic references and definitions reside inside military doctrine, we are still missing any single specific and standardized procedure for Target System Analysis on non-state actors, which is strongly different from those conventional forces for which our traditional means, actions and TSA procedures were designed a long time ago…
Additionally, and based on both its structural and scientific limitations, the traditional CARVER methodology is not adequately covering the needs for target/audience selection and prioritization on non- state actors and other human networks… and, although still working for vulnerability assessment, CARVER is about eighty years old and too lethally oriented.
Accordingly, a modern, and effective Attack the Networks approach would need an alternative updated tool for target/audience selection and prioritization: it is recommended for it not to only look at the characteristics of the target itself, but also considering the action to conduct and the effects to achieve.
That is why some brave Attack the Networks experts are developing a new approach to the prioritization of targets and audiences, so: In the aim of increasing the scientific approach and objectivity of the analysis, the number of criteria is increased to fifteen (instead of the six from CARVER), and their respective quantification through values (1-5) is intended to be clearly and accurately defined.
In that way, the proposed criteria are as follows:
• (Related to TARGET) Reactivity, Sensitivity, Identification, Counter Measures & Resistance.
• (Related to ACTION) Easy, Cost-Effective, Foreseeable, Surgical & Attribution.
• (Related to EFFECT) Exploitability, Persistence, Evaluability, Sinergy & Impact (see Figure 4).

Figure 4: Attack the Networks proposed model for selection & prioritization of targets/audiences. (Source –C-IED CoE)
Running towards solutions
As already stated, the 21st Century needs updated solutions for those problems deriving from new threat scenarios and evolving adversary human networks, so here is the challenge for Attack the Networks.
Only if we are successful in developing advanced analytical tools specifically adapted to non-state actors instead of those designed for conventional forces, will there be an opportunity to anticipate and face the threat from violent extremist organizations.
Maybe those Attack the Networks initiatives on developing human network characterization, procedures on Target System Analysis for non-state actors, refined methodology for target/audience selection and prioritization, and maybe something additional on integration of effects on human networks could look like a chimera, but it is little by little transforming into some drafts which could maybe result in handbooks or manuals: the close future will maybe show the potential outputs to us… who knows!
As someone said: “It was considered as something impossible until one guy who was not aware of that, just analyzed the problem, tried to find solutions, and finally was able to…” ■
“The truth isn’t always going to be handed to you. Sometimes, you have to fight for it.” `
(Marisa Urgo, in her book “The Gravity of Missing Things” first published in 2002)
FOOTNOTES
- At least from official NATO perspective: a careful and complete (further than a direct translation from the title) reading of AJP- 3.15 “Allied Joint Doctrine for Countering Improvised Explosive Devices C-IED” could maybe support understanding about the subject matter.
- Again, see obsolete and current versions of AJP-3.15 “Allied Joint Doctrine for Countering Improvised Explosive Devices C-IED”.
- UNIDIR Counter-IED Capability Maturity Model and Self-Assessment Tool, 24 June 2020.
- Translatable as “Nothing is more dangerous than an idea when it is the only one you have.” (Emile Chartier, aka “Alain”, in his book “Propos sur la religion, Un nouveau Dieu”, 20 juillet 1930.
- Source: C-IED CoE.
- Maybe except for United States Special Operations Command (USSOCOM) and British Intelligence inside the whole NATO framework.
REFERENCES
- BRENNET B.T. (2018) – “Understanding, Assessing, and Responding to Terrorism: Protecting Critical Infrastructure and Personnel”. John Wiley & Sons.
- BORGATTI S.P., EVERETT M.G. & JOHNSON J.C. (2018) – “Analyzing Social Networks”. SAGE Publications Ltd.
- BURKS R. (2017) – “CARVER 2.0: integrating the Analytical Hierarchy Process’s multi-attribute decision-making weighting scheme for a center of gravity vulnerability analysis for US Special Operations Forces”. Journal of Defense Modeling and Simulation.
- C-IED CoE – Attack the Networks study draft on Procedures for Support to Effects and Target System Analysis over Non-state Actors and other Human networks, 2023.
- CLARK R.M. (2022) – “Intelligence Analysis: A Target- Centric Approach”. CQ Press.
- CURTIS E. PINNIX, JR (2021) – “Specialized Analytic and Targeting Study. A Methodology and Approach for Conducting Faster Full-Spectrum Targeting” (Joint Force Quarterly 103). National Defense University Press.
- FERREIRA A (2019) – “Vulnerability analysis in critical infrastructures: A methodology”. War Studies University, Security and Defence Quarterly.
- FOX W.P. & HANSBERGER J. (2018) – “Methodology for targeting analysis for minimal response”. Journal of Defense Modeling and Simulation.
- LABAJ L. & BENCIE L. (2018) – “The CARVER Target Analysis and Vulnerability Assessment Methodology: A Practical Guide for Evaluating Security Vulnerabilities”. Security Management International.
- MITCHELL T.E. (2020) – “Forging the Center of Gravity”. Marine Corps gazette.
- NATO STANDARD (2021) – “AJP-3.9 Allied Joint Doctrine for Joint Targeting”. NATO Standardization Office (NSO). NATO STANDARD (2017) – “AIntP-13 Doctrine for Human
- Network Analysis and support to Targeting (HNAT)”. NATO Standardization Office (NSO).
- PHERSON R.H. & HEUER R.J. (2020) – “Structured Analytic Techniques for Intelligence Analysis”. CQ Press.
- ROORDA M (2015) – “NATO’s targeting process: ensuring human control over (and lawful use of) ‘autonomous’ weapons”. In A. P. Williams, & P. D. Scharre (Eds.), Autonomous systems: issues for defence policymakers (pp. 152-168). NATO HQ SACT.
- SCHNAUBELT C.M. (2014) – “VAM Vulnerability Assessment Method Pocket Guide. A Tool for Center of Gravity Analysis”. RAND Corporation, Washington D.C.
- U.S. Department of Defense Joint Chiefs of Staff (2003) – “Joint Publication 2-01.1 Joint Tactics, Techniques, and Procedures for Intelligence Support to Targeting”. CreateSpace Independent Publishing Platform.
- U.S. Department of Defense Joint Chiefs of Staff (2003) – “Joint Publication 3-05.2 Joint Tactics, Techniques, and Procedures for Special Operations Targeting and Mission Planning”. CreateSpace Independent Publishing Platform.
- U.S. Department of Defense Joint Chiefs of Staff (2016) – “Joint Publication 3-25 JP 3-25 Countering Threat Networks”. CreateSpace Independent Publishing Platform.
- U.S. Department of Defense Joint Chiefs of Staff (2014) – “Joint Publication 3-26 JP 3-26 Counterterrorism”. CreateSpace Independent Publishing Platform.
- U.S Department of the Navy, Headquarters United States Marine Corps (2016) – “MCTP 2-10B, MAGTF Intelligence Production and Analysis.” www.marines.mil
- WOLF, J.B. (1978) – “Target Analysis Part 1 – Techniques and Practices of Terrorist Groups (From Clandestine Tactics and Technology – A Technical and Background Intelligence Data Service, Volume 4). U.S. Department of Justice.
- YOE C. (2019) – “Principles of Risk Analysis: Decision Making Under Uncertainty”. CRC Press.
Disclaimer
This article does not represent the opinion of any national or multinational organisation; its whole content should only be considered as the opinion of the author. As all the information has been obtained from open sources, potential mistakes could have been made during the research process. Please feel free to send your comments, corrections and inputs to the author; they will be highly appreciated.
ABOUT THE AUTHOR
Lieutenant Colonel Jose M Rufas graduated from the Spanish Army Military Academy in 1993. He was commissioned into the C-IED Centre of Excellence as Head of the Defeat the Device Branch in August 2016, and currently holding a post of Chief of Attack the Networks Branch. As a Military Engineer Officer, his background has been mainly based on Explosive Ordnance Disposal activities in the Spanish Army and C-IED staff issues at the multinational headquarters. In addition to his EOD Operator / EOD Officer education, he attended some other military courses regarding Parachuting, Army Staff, Information Operations, War College General/ Joint Staff, Military Search, Technical Exploitation Operations, Weapons Intelligence Team, Exploitation Laboratories, Homemade Explosives and other C-IED courses. His operational assignments include Bosnia and Herzegovina (3), Afghanistan (3), Republic of Ecuador, Iraq and Uganda.
E-mail: [email protected]
Download PDF: 56-63 Jose Rufas article – HUMAN NETWORK CHARACTERIZATION – COUNTER-IED REPORT, Autumn 2023

